“I’m not watching anymore,” I say — while watching. Every week I tell myself: “That’s it. I’m done. No more Philippine news. I need peace, serenity, and maybe a working blood pressure.” Then I open Twitter. Then I see a headline like “Cybersecurity Budget Slashed in Favor of New Dancing Fountain.” And suddenly I’m yelling at my phone like I
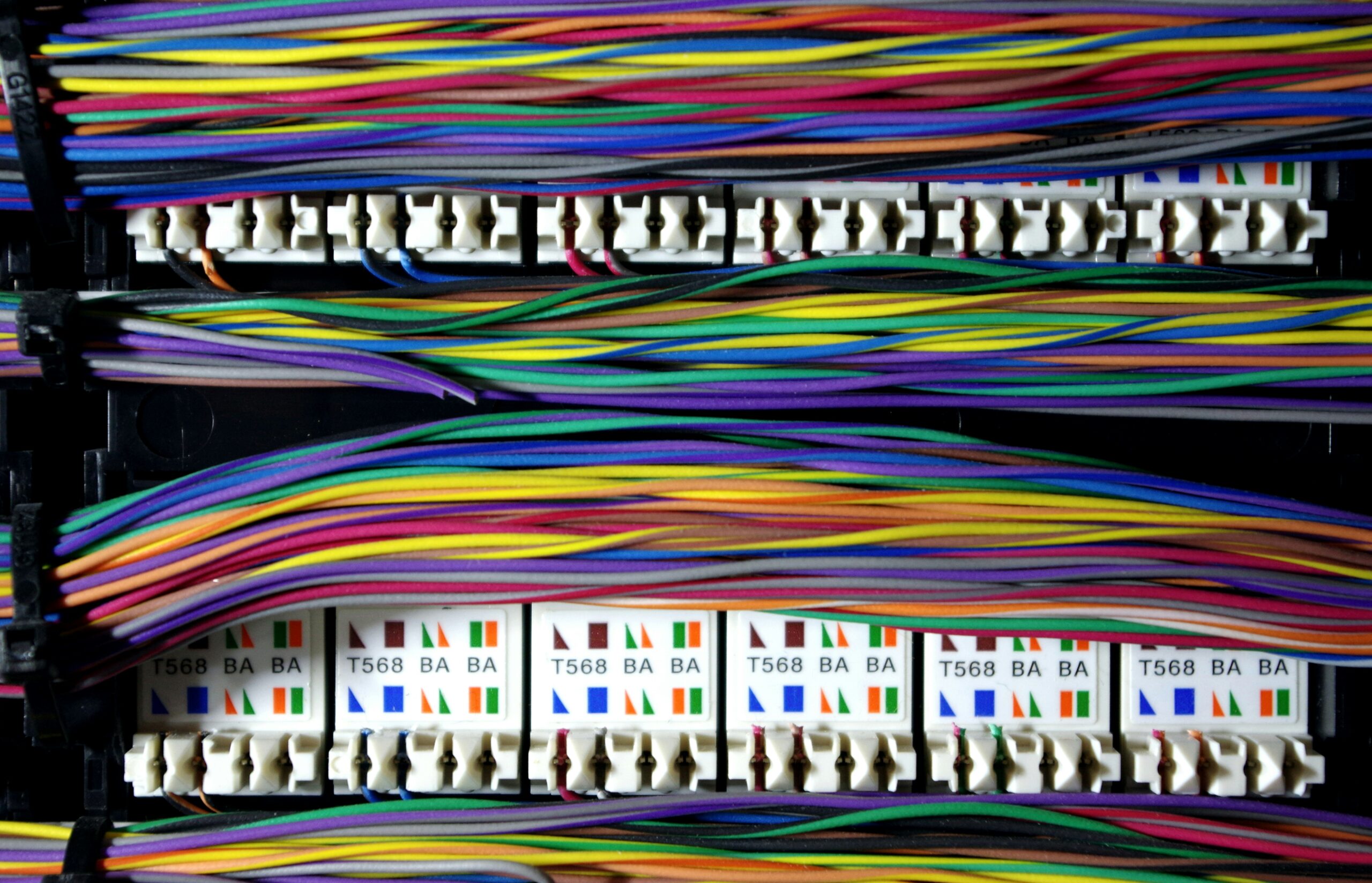
Sysadmin. Network guy. GIS nerd. Database whisperer. Zoom host. Coffee runner. You ever look at a problem and think, “Whose job is this?”And then realize — oh right — it’s yours. Welcome to the chaotic, caffeine-fueled world of being a solo IT department. I don’t just wear many hats. I’m running a whole hat store. My official job title? Unclear.
I left the Philippines in 2013. Since then, I’ve lived in the U.S., discovered the joy of functioning public libraries, and gotten spoiled by tap water you can actually drink. But even after more than a decade away, my screen still lights up with poverty maps of the Philippines—every shade of red feels personal. It’s as if the map knows
Plot twist: It was one of mine the whole time. So there I was — mid-coffee, mid-ticket, mid-existential crisis — when I looked at my Wi-Fi dashboard and saw something terrifying: Two networks.Same SSID.One was mine.The other? An imposter. My first thought? “It’s happening. Evil twin attack. Shut it all down. Tell my wife I love her.” I leapt into
So I sat down to study—again—and somehow ended up face-to-face with my Darth Vader figure wondering, “Shouldn’t you be on a better shelf?” Next thing I knew, I was wrist-deep in microfiber cloths, battling dust bunnies like they were stormtroopers with bad aim. Because yes, I took another “quick break” from studying and ended up rearranging my toy collection again.
(Especially If You Work in a Public Utility Agency) Let’s not sugarcoat it: public utility agencies are prime targets. Not because we’re hoarding national secrets, but because attackers know we’re stretched thin, glued to outdated systems, and busy keeping things running while everyone else enjoys power, water, and a working commute. So what should cybersecurity awareness training actually include? Here’s
(Now With Less Bureaucracy, More Actual Defense) So you want to protect the Philippines from cyber threats?Nice. Us too. But here’s the catch:We can’t keep saying “we need better cybersecurity” and then hand over the entire IT budget to (1) antivirus software from 2009 and (2) a printer that keeps printing sideways. It’s time we build a starter pack —
Some outages are caused by power failures. Others by network issues.And then there are the ones caused by a vendor who decided—without telling you—to deactivate the literal lifeline of your organization. That was my Wednesday. Right before Juneteenth. The Main Line: Disconnected The District’s main customer service number—the one printed on every bill, posted on the website, and used for
Because we can Google it ourselves, thank you very much. Let’s not sugarcoat it: Philippine cybersecurity is behind. Behind in funding. Behind in skills development. Behind in taking threats seriously until they hit us square in the NBI database. And what’s the usual response? “Hire a foreign consultant!”Preferably someone who charges six figures, presents a fancy PowerPoint, and whose only
Let’s talk about something serious — not in a boring, policy-wonk kind of way, but in a “we should actually care about this before things go south” kind of way. Because while we’re busy arguing online, stuck in traffic, or watching another Senate hearing that feels more like a teleserye, the rest of the world is playing 4D chess with